- Solves: 35
Somebody asked for more crypto challenges, so we made one in the middle of the night. Now you better solve it.
https://35c3ctf.ccc.ac/uploads/post_quantum-377f0fc6e7eb3afcda72921849d7c2cb.tar.gz
- Solves: 35
The NSA gave us these packets, they said it should be just enough to break this crypto.
Difficulty estimate: medium
- Solves: 0
Infoleak only they said, no need to patch right?
Challenge runs at 35.207.172.161:4444
The shell provided is the one running remotely, it has debug symbols.
we built the shell on the follow commit with path:
git clone -b release https://github.com/mozilla/gecko-dev.git --depth 100 git checkout 05ff5c64e02f06146e74bd19136ae96117f5a2de git apply ../diff.patchDifficulty estimate: hard
- Solves: 3
Krautflare workers are the newest breakthrough in serverless computing. And since we're taking security very seriously, we're even isolating customer workloads from each other!
For our demo, we added an ancient v8 vulnerability to show that it's un-exploitable! See https://bugs.chromium.org/p/project-zero/issues/detail?id=1710 for details. Fortunately, that was the last vulnerability in v8 and our product will be secure from now on.
Files at https://35c3ctf.ccc.ac/uploads/krautflare-33ce1021f2353607a9d4cc0af02b0b28.tar. Challenge at:
nc 35.246.172.142 1Note: This challenge is hard! It's made for all the people who asked for a hard Chrome pwnable in this survey at https://twitter.com/_tsuro/status/1057676059586560000. Though the bug linked above gives you a rough walkthrough how to exploit it, you'll just have to figure out the details. I hope you paid attention in your compiler lectures :). Good luck, you have been warned!
- Solves: 30
-
The container is built with the following important statements
FROM ubuntu:18.04 RUN apt-get -y install python3.6 COPY build/lib.linux-x86_64-3.6/Collection.cpython-36m-x86_64-linux-gnu.so /usr/local/lib/python3.6/dist-packages/Collection.cpython-36m-x86_64-linux-gnu.soCopy the library in the same destination path and check that it works with
python3.6 test.pyChallenge runs at 35.207.157.79:4444
Difficulty: easy
- Solves: 2
Here is another linux user namespaces challenge by popular demand.
For security reasons, this sandbox needs to run as root. If you can break out of the sandbox, there's a flag in /, but even then you might not be able to read it :).
The files are here: https://35c3ctf.ccc.ac/uploads/namespaces-a4b1ac039830f7c430660bc155dd2099.tar Service running at:
nc 35.246.140.24 1- Hints:
You'll need to create your own user namespace for the intended solution.
- Solves: 3
Remember the Nokia 1337 from 31C3? This time we have a real target for you!
Note: There is a giant readme in the provided archive. Make sure you read it and try everything locally first. After you have your exploit, launch it against the remote infrastructure and get to the real meat!
Note 2: The UI crashes when you select a phone book entry and select "Options". This is not intended and an oversight by the author but isn't relevant to the solution to the challenge. So just don't hit that button.
- Hints:
To avoid confusion: The target phone can reach external hosts on the internet and has netcat installed.
- Solves: 3
Sandboxes are fun!
Get the challenge files here and submit your exploits here. Files for the VM setup can be found here, they are the same as for the WebKid challenge.
The uploaded binary will be run with the following sandbox profile:
(version 1) (deny default) (import "system.sb") (allow process-exec (literal "/path/to/exploit")) (allow process-fork) (allow mach-lookup (global-name "net.saelo.shelld")) (allow mach-lookup (global-name "net.saelo.capsd")) (allow mach-lookup (global-name "net.saelo.capsd.xpc"))Password for the encrypted VM image is the flag for "sanity check".
Difficulty estimate: medium
- Solves: 1
We improved our SQL server from last year. Thanks pasten for telling us about a bug it had. We fixed it.
Running at 145.239.149.235:1337
Challenge is running on fully updated Windows 10 RS5 (Build 1809). You may try to use one of the images from [1], they did not work for us but good luck.
Challenge is running with low IL and served via
socat -T180 tcp4-l:1337,fork exec:./pwndb.exein a WSL bash shell.
Also, because Windows 10 sucks as a server system (although surprisingly 1809 sucks way less than 1709), we might kill all pwndb.exe processes every 10 minutes or so. So if your exploit fails, please try again. If your exploit takes much longer than a few minutes, please let us know and we might be able to disable the watchdog temporarily.
There is no intended bug in the SQL parser, so you may just trust the sqlparser.h file. Oh and we noticed that people were exploiting a red herring bug we thought was unexploitable. Thanks for telling us, it's fixed.
Flag is in
C:\flag.txt. Don't assume the challenge process is allowed anything other than to read this file.Difficulty estimate: hard
HINT:
- Solves: 167
Build with my new packer framework. Do you likes zeros in weird places? Try this!
(Password does not contain 35C3_, prepend before submitting flag
35C3_${extracted_password}) Guest challenge by Qubasa.Difficulty estimate: medium
- Solves: 82
As every year, can you please decode this for me?
- Solves: 97
https://35c3ctf.ccc.ac/uploads/corebot-640d3c582340e647d72e1dd9418a3fd6
Difficulty estimate: easy
Guest challenge by Jesko / rattle.
UPDATE: Challenge binary replaced. Apologies for the inconvenience.
- Solves: 2
Note: This challenge is only solvable after newphonewhodis
After you compromised the phone, you need to dig deeper. There is a flag on the SIM card in file 0x4333 which you need to get.
- Hints:
Here is a binary with symbols of the SIM card you need to get the requested file from.
- Solves: 54
Can you help this restaurant Stack the right amount of Eggs in their ML algorithms?
Guest challenge by Tethys.
Note that you need to send a shutdown(2) after you sent your solution. The nmap netcat will do so for you, e.g.:
ncat 35.246.237.11 1 < solution.xml/usr/bin/ncat --help | grep -n 1 Ncat 7.60 ( https://nmap.org/ncat )
Files here: https://35c3ctf.ccc.ac/uploads/juggle-f6b6fa299ba94bbbbce2058a5ca698db.tar
- Solves: 18
veni, vidi, notifici
Notes: - only chmod, no touch - no root user, please - tar --no-same-owner -xhzf chall.tar.gz
HINT: The graph is a move graph for a certain type of chess piece.
- Solves: 33
Guest challenge by Kokjo. Enjoy!
Files at https://35c3ctf.ccc.ac/uploads/permute-b3e77892990db2b055aebdc3916426c1.tar
- Solves: 612
This could help with some other challenges.
35P3_hfr_guvf_gb_REDACTED
- Solves: 5
Check out my web-based filemanager running at https://filemanager.appspot.com.
The admin is using it to store a flag, can you get it? You can reach the admin's chrome-headless at:
nc 35.246.157.192 1
- Solves: 18
https://35.207.157.20/
Difficulty estimate: easy
Challenge redeployed with new flag at 22:45 UTC.
UPDATE: The challenge has been redeployed with a small bugfix and updated keys/flags. This output was leaked before, so here it is for everybody: https://35c3ctf.ccc.ac/uploads/lambda-leak.txt
- Solves: 209
PHP's unserialization mechanism can be exceptional. Guest challenge by jvoisin.
Files at https://35c3ctf.ccc.ac/uploads/php-ff2d1f97076ff25c5d0858616c26fac7.tar. Challenge running at:
nc 35.242.207.13 1
- Solves: 2
Go make some posts.
Hint: flag is in db
Hint2: the lovely XSS is part of the beautiful design and insignificant for the challenge
Hint3: You probably want to get the source code, luckily for you it's rather hard to configure nginx correctly.
- Solves: 18
You can't draw this. But dive into!
http://35.207.101.144/
Difficulty estimate: easy
- Hints:
The first step of the challenge is stego. Don't try to zoom, use a magnifying glass.
- Solves: 3
Web 3.0 is the future. You can build anything with it, no matter how useful.
Hint: If you are stuck, play around with the
/executeendpoint and carefully read the responses.- Hints:
At least two different kinds of properties of instructions are encoded on the type level, and proven via the type checker. But are all of these properties sufficiently strict to ensure safety?
- Solves: 2
Please escape VirtualBox. 3D acceleration is enabled for your convenience.
No need to analyze the 6.0 patches, they should not contain security fixes.
Once you're done, submit your exploit at https://vms.35c3ctf.ccc.ac/, but assume that all passwords are different on the remote setup.
Challenge files. Password for the encrypted VM image is the flag for "sanity check".
UPDATE: You might need to enable nested virtualization.
Hint: https://github.com/niklasb/3dpwn/ might be useful
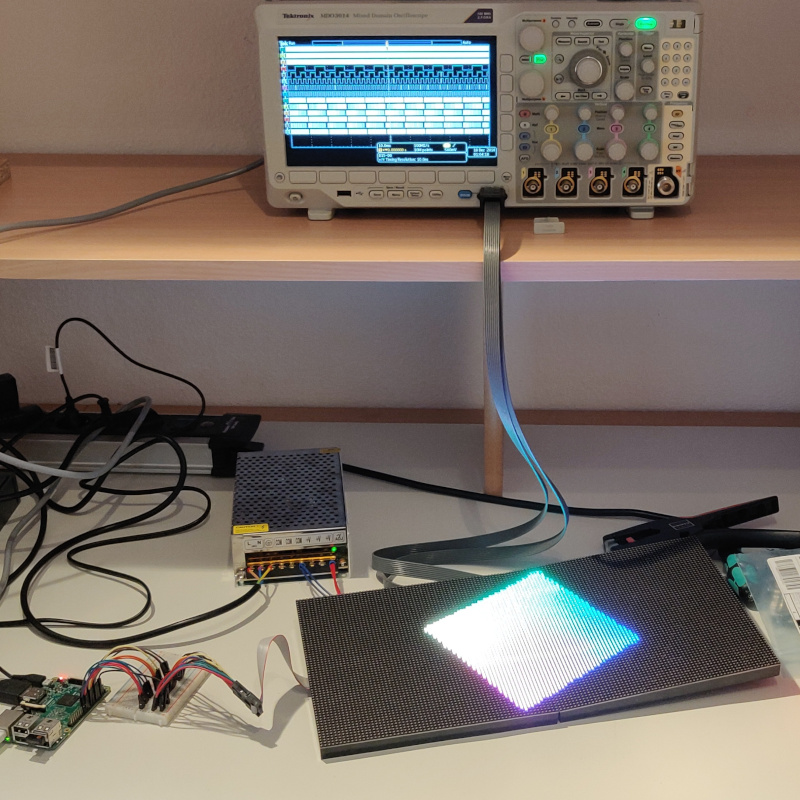
Hint 2: this photo was taken earlier today at C3
Difficulty estimate: hard
- Solves: 0
I heard nowadays the cool kids like Donald J. Trump use ExpressionEngine to express themselves on the Internet. After all, the "Best CMS" is just about good enough for the bestest presidents.
This morning I set up a default install and gave it a try, do you like it?
PSA: dont dirbuster it... you won't find anything
Info: Here are a few deployment details: https://35c3ctf.ccc.ac/uploads/express_yourself_deployment_details.txt in case you got confused why the system directory might be missing.
Hint: flag is in db
Hint2: challenge was probably a bit miscategorized in the "web" category, it belongs into the zajebiste category. There are no hidden files or anything, see the deployment script. you can set up the same environment locally and pwn it. no need to bruteforce anything, good luck
- Solves: 5
Can you bypass the patch? https://hackerone.com/reports/397478
https://vms.35c3ctf.ccc.ac/
https://35c3ctf.ccc.ac/uploads/keybase-5919154ffe36b7f1731af9d787c95394.tar.gz
Difficulty estimate: medium
UPDATE: The VM is running the current version of Keybase, 2.12.2
UPDATE 2: Apparently keybase decided to release a new version of the macOS client today, which is an update from 2.12.2 to 2.12.4. Don't install it for now if you have the choice. The challenge is running 2.12.2. We will soon provide a QEMU disk image with the old version in case it is relevant.
UPDATE 3: Find the keybase VM run script and images (version 2.12.2) at https://35c3ctf.ccc.ac/uploads/keybase-vm-a4f723ef126f84162a324232b1cef696.tar.gz
The image files can be downloaded via torrent from https://35c3ctf.ccc.ac/uploads/e3a1407a71362380fe0bc91b91d8f43964ee51b4.7z.torrent and the password is the flag for "sanity check"
- Solves: 11
logrotate is designed to ease administration of systems that generate large numbers of log files. It allows automatic rotation, compression, removal, and mailing of log files. Each log file may be handled daily, weekly, monthly, or when it grows too large. It also gives you a root shell.
For your convenience, I added a suid binary to run cron jobs. Enjoy. Files at: https://35c3ctf.ccc.ac/uploads/logrotate-6c103367e3c15cb6873403e16b38f540.tar And get your shell here:
nc 35.242.226.147 1
- Solves: 3
Fuzz all the things. Idea by joernchen, please credit all found bugs to him!
https://35c3ctf.ccc.ac/uploads/sequence-afcf267d78429b4a36dca5bd12bdf45e.tar.gz
Running at: 35.207.188.80:1337
Difficulty estimate: hard
- Hints:
Read the README until the very end. Also, make sure you use the exact same libc that is provided (it is a non-default build, again see README).